Vendor Risk Management for Healthtech Startups
Mar 24, 2026
Every healthtech company depends on vendors. Cloud infrastructure. Analytics platforms. EHR integrations. AI tooling. Payment processors. The stack grows as the product scales, and with every vendor added, the company takes on a new layer of legal and regulatory exposure.
Most healthtech teams manage vendor relationships commercially price, service level, renewal timing. The legal and risk layer receives far less attention until something forces it: a security incident, a diligence process, a regulatory inquiry. By that point, the gaps in vendor agreements are no longer theoretical.
Why Vendor Risk Is Different in Healthtech
In most industries, a vendor failure is an operational problem. In healthtech, it can become a regulatory one. When a vendor processes, stores, or accesses protected health data, the downstream company inherits obligations to patients, to regulators, and to the enterprise customers it has made commitments to.
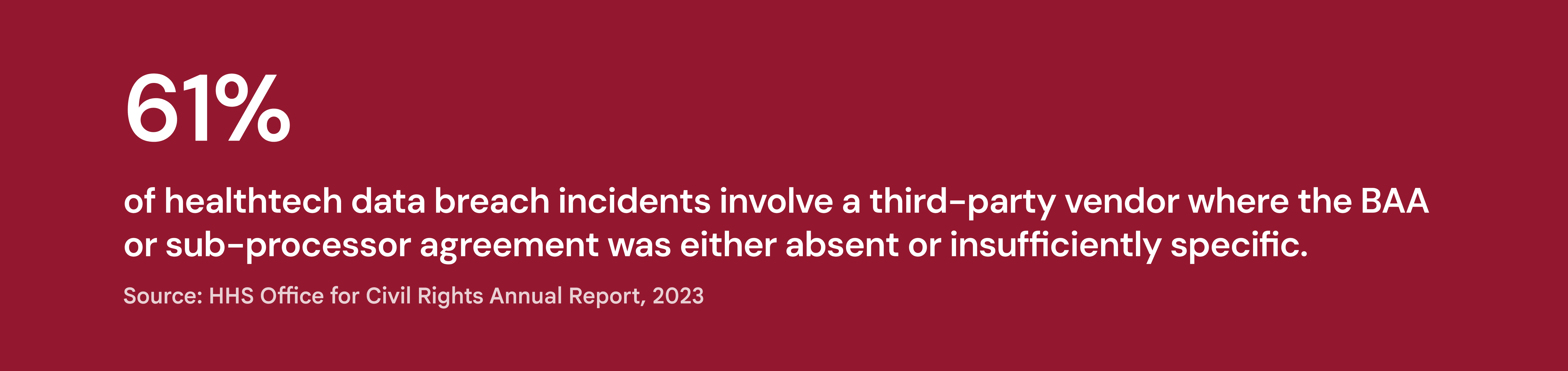
HIPAA Business Associate Agreements are the most visible layer. But BAAs are often treated as a checkbox rather than a substantive risk management tool. The question is not whether a BAA exists, it is whether the obligations in that BAA are specific, enforceable, and aligned with the actual data flows between the parties.
The Four Gaps That Create the Most Exposure
Sub-processor oversight. If a vendor uses its own sub-processors to deliver service, and those sub-processors access or process health data, the chain of obligation runs through. Vendor agreements frequently omit the ability to audit, approve, or even identify sub-processors. That gap leaves the healthtech company with downstream exposure it cannot manage.
Breach notification timelines. HIPAA requires breach notification within 60 days of discovery. Many enterprise customer contracts require notification within 72 hours or less. If vendor agreements do not require notification timelines that align with these downstream obligations, the company will be unable to meet its own commitments when a vendor incident occurs.
Security standard specificity. Agreements often state that vendors will maintain "industry standard security." Without defining the specific frameworks, certifications, or audit rights that standard implies, the language is unenforceable. When a buyer asks whether vendor security commitments are measurable and verifiable, a vague representation's answer is not acceptable.
Data exit and deletion. What happens to patient data when a vendor relationship ends? Termination clauses routinely address payment and notice mechanics but omit data return timelines, verified deletion protocols, and audit continuity. In regulated environments, those obligations do not end when the contract does.
What Proactive Vendor Risk Management Looks Like
Companies that manage vendor risk well do not treat it as a legal review exercise. They treat it as an ongoing mapping function. Every new vendor gets assessed against the same framework. Existing vendors get reviewed when the product architecture changes, when data flows expand, or when a regulatory update affects the relevant standards.
Lexapar maps vendor contractual obligations against actual data flows and product architecture, tracks sub-processor exposure across the full stack, and surfaces misalignment before it becomes a diligence finding or a regulatory issue. When scrutiny arrives, the company can demonstrate control rather than reconstruct it.
Map your vendor exposure before a regulator or investor does
Lexapar gives healthtech teams visibility into vendor risk across the full contract stack
